ModSecurity is a web application firewall. It blocks the incoming web request depends on the added ruleset. Using ModSecurity, you can protect your web application against attacks like session hijacking, SQL injection, cross-site scripting, etc. In this article, we will install the mod security version 3. It is faster than the previous versions.
Please refer to the following steps to install ModSecurity 3 in cPanel. We assume you have root access to the server, and also Easyapache4 is installed on it.
- Login to your server using SSH.
- Run the below command to install the EasyApache4 experimental repository.
yum install ea4-experimental
- Please uninstall the mod security2 if you have already installed it on the server.
yum remove ea-apache24-mod_security2
- Run the below command to install connectors that allows ModSecurity to work with a web server.
- For Apache
yum install ea-modsec30-connector-apache24
- For Nginx
yum install ea-modsec30-connector-nginx
WHM Part
- Login to your WHM Panel.
- Inside the software, click on the EasyApache 4.

- Click on the customize button.

- Go to the additional packages and ensure the connector is installed. If you are working for apache, ensure that modsec30-connector-apache24 is installed. For Nginx, you require modsec30-connector-nginx.

- Click on the Next, review, and provision button to complete the installation.

- Now, install the OWASP Core Rule Set using the below command.
yum install ea-modsec30-rules-owasp-crs
ModSecurity Confiuration
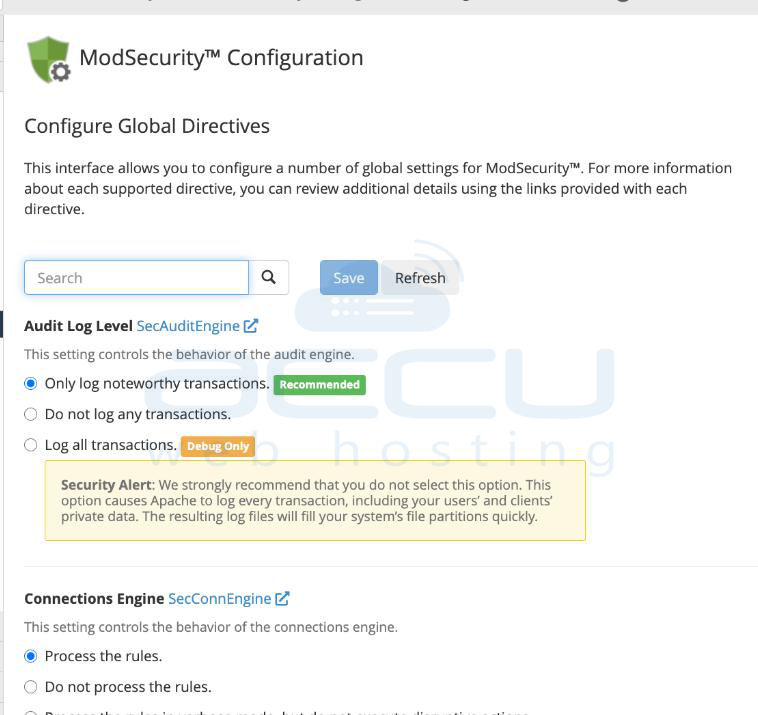
At ModSecurity configuration, you can set up several global settings. It allows configuring the behavior of the audit log, rules engine, and connection engine.
To learn more about these configuration options, please refer to the ModSecurity configuration documentation.
ModSecurity Tools
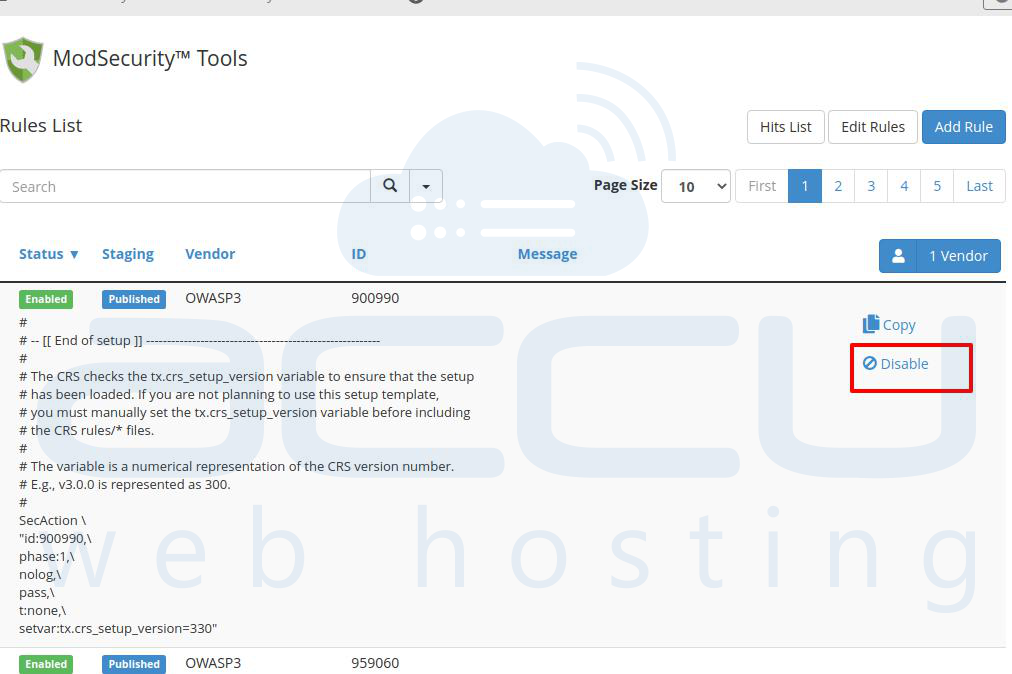
ModSecurity Tools allows monitoring and configuring the firewall’s rules. You can find all the rules here and also activate/deactivate rules as per the requirement. It also allows adding a new rule. Please refer to SecRules language for more details.
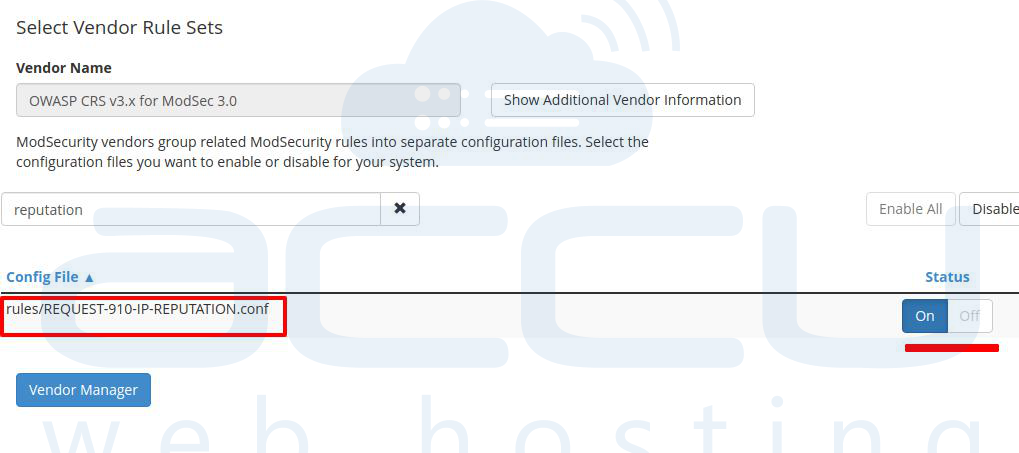
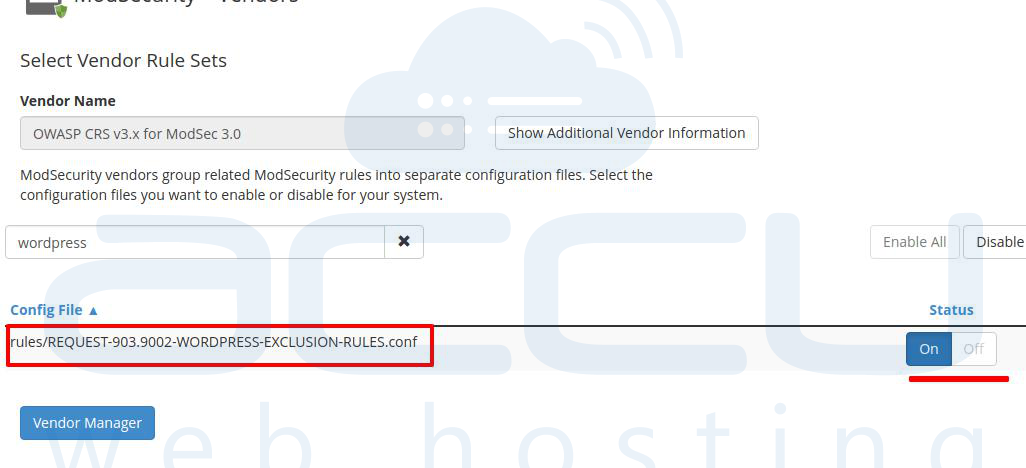
ModSecurity Vendors
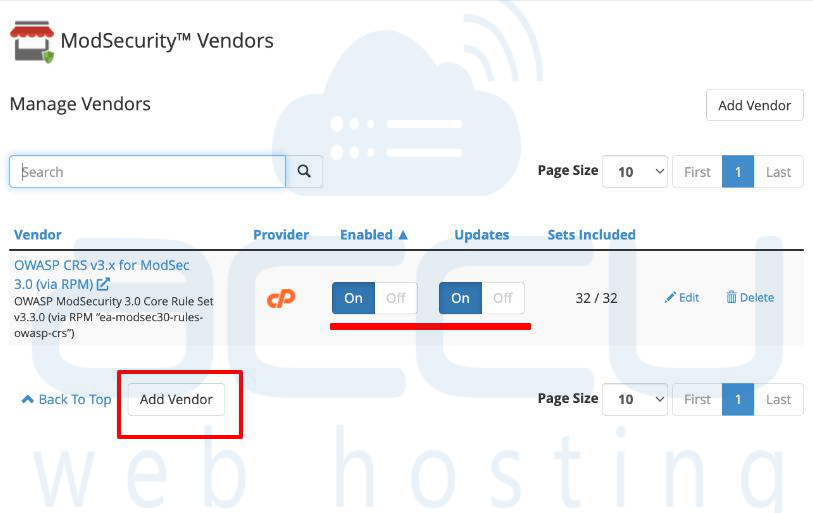
ModSecurity Vendors allows adding and managing various rule sets. You can see the OWASP CRS rule set that we have installed. You can activate or deactivate it from here. You can also edit or exclude the rule set like IP reputation, Wordpress exclusion, etc.