What is DMARC?
DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol that utilizes widely used SPF and DKIM protocols to determine, whether or not a given message is legitimately sent from the sender, and what to do if it isn’t. The DMARC record adds the reporting functionality in existing DKIM and SPF records, allowing senders and receivers to improve protection of the domain from spoofed spams and keep them out of people's inboxes.
How DMARC Works?
Like other DNS records (SPF, A record, CNAME, DKIM, etc.), DMARC record is published and tells receiving server, whether or not to accept an email from a particular sender. DMARC can fit into an organization’s existing inbound email authentication process and helping email receivers determine if the received email “aligns” with what the receiver knows about the sender. When a received message don’t align, DMARC includes the guidance on how to handle such “non-aligned” messages. Assuming that the email receiver has deployed the SPF and DKIM along with its own spam filters, the email flow may look something like this.
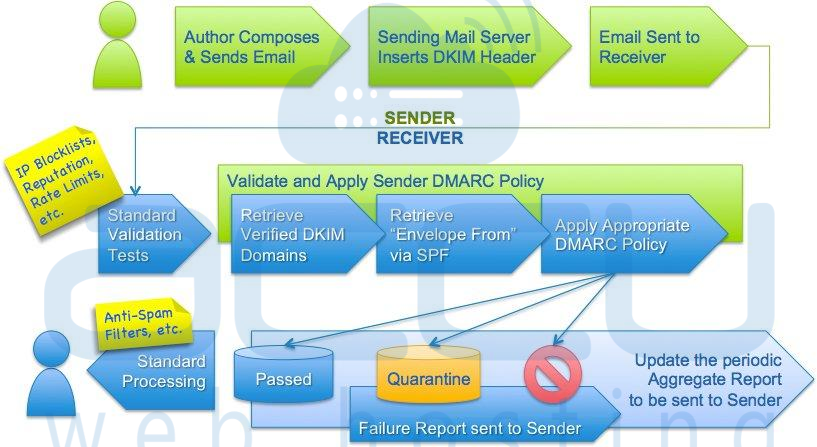
- User composes an email and send with the DKIM header inserted by the sender server.
- DMARC matches the header from domain name with the envelope from domain name used during an SPF record check.
- DMARC matches the header from domain name with the d= domain name in the DKIM signature.
- To pass the DMARC authentication, received message must pass the SPF authentication/ alignment and/or DKIM authentication/alignment. When the message fails both SPF/SPF alignment and DKIM/DKIM alignment, the DMARC will get failed and it will instruct email providers on how to handle unauthenticated mail via a DMARC policy. According to the DMARC policy you set, senders can either:
- Monitor all mail ensuring all legitimate mail are authenticating properly without interfering with the delivery of messages that fail DMARC.
- Quarantine messages that fail DMARC.
- Reject messages that fail DMARC.
DMARC Tags
DMARC policies are published in the DNS as a text (TXT) records and announce what an email receiver should do with non-aligned. Consider the following example.
"v=DMARC1;p=reject;pct=100;rua=mailto:[email protected]"
Above example tells the sender that, the receiver outright reject all non-aligned messages and send a rejection report to a specified email address. When you are just testing the DMARC policy, you can replace “reject” with “quarantine” which would tell the receiver they shouldn’t necessarily reject the message, but consider quarantining it. Following chart illustrates the DMARC records extensible tags.
| Tag Name | Purpose | Sample |
| v | Protocol version | v=DMARC1 |
| pct | Percentage of messages subjected to filtering | pct=20 |
| ruf | Reporting URI for forensic reports | ruf=mailto:[email protected] |
| rua | Reporting URI of aggregate reports | rua=mailto:[email protected] |
| p | Policy for organizational domain | p=quarantine |
| sp | Policy for subdomains of the OD | sp=reject |
| adkim | Alignment mode for DKIM | adkim=s |
| aspf | Alignment mode for SPF | aspf=r |
Create DMARC Record
Once you setup the SPF and DKIM records, you can configure the DMARC by following below DMARC wizard with appropriate name and value. Again, DMARC policies are published in the DNS as text (TXT) record. So once your DMARC record is ready, you can add it as a TXT record in your DNS zone.
DMARC Wizard
→ Looking to add dmarc record in cloudflare? Please refer to add dmarc in cloudflare for more details.
